7. Misbehaving Clients:
Clients that form unauthorized Wi-Fi connections of any type, whether accidentally or intentionally, put themselves and corporate data at risk. Some enterprises use Group Policy Objects to configure authorized Wi-Fi connections and prevent end-user changes. Others use host-resident agents and/or WIPS to monitor Wi-Fi client activity and disconnect high-risk connections. However, many businesses (especially SMBs) still depend on end-users to connect only to known, authorized wireless APs. Given ubiquitous deployment, longer reach, and broader consumer electronics integration, accidental or inappropriate Wi-Fi connections have never been easier. If you haven’t already taken steps to stop Wi-Fi client misbehavior, start now.
8. Endpoint Attacks:
Now that over-the-air encryption and network-edge security have improved, attackers have refocused their attention on Wi-Fi endpoints. Numerous exploits have been published to take advantage of buggy Wi-Fi drivers, using buffer overflows to execute arbitrary commands – sometimes at ring 0 (high-privilege kernel mode). Automated attack tools like Metasploit can now be used to launch Wi-Fi endpoint exploits with minimal effort. Although vendors do (usually) patch these bugs once discovered, Wi-Fi driver updates are not distributed automatically with OS updates. To protect your workforce, track Wi-Fi endpoint vulnerabilities (for example, using WiFiDEnum) and keep your Wi-Fi drivers up-to-date.
9.Evil Twin APs:
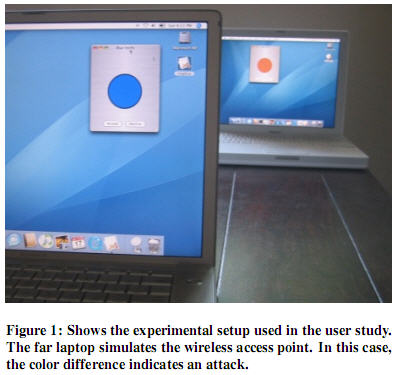
Fraudulent APs can easily advertise the same network name (SSID) as a legitimate hotspot or business WLAN, causing nearby Wi-Fi clients to connect to them. Evil Twins are not new, but easier-to-use hacker tools have increased your risk of running into one. Tools like Karmetasploit can now listen to nearby clients, discover SSIDs they’re willing to connect to, and automatically start advertising those SSIDs. Once clients connect, DHCP and DNS are used to route client traffic through the Evil Twin, where local (phony) Web, mail, and file servers execute man-in-the-middle attacks. The only effective defense against Evil Twins is server authentication, from 802.1X server validation to application server certificate verification.
10.Wireless Phishing:

In addition to the above man-in-the-middle application attacks, hackers continue to develop new methods to phish Wi-Fi users. For example, it’s possible to poison Wi-Fi client Web browser caches, so long as the attacker can get into the middle of a past Web session – such as by using an Evil Twin at an open hotspot. Once poisoned, clients can be redirected to phishing sites long after leaving the hotspot, even when connected to a wired enterprise network. One technique for mitigating this threat is to clear your browser’s cache upon exit. Another possibility is to route all hotspot traffic (even public) through a trusted (authenticated) VPN gateway.


